Test #1: Direct test of the firewall (IPv4)
Step 1:
Install beSTORM and its IPv4 Module on a server that is not otherwise in use or on a network.
Confirm or install a network device driver such as Winpcap:
http://www.winpcap.org/install/default.htm
Start NPF service at cmd line: sc start npf
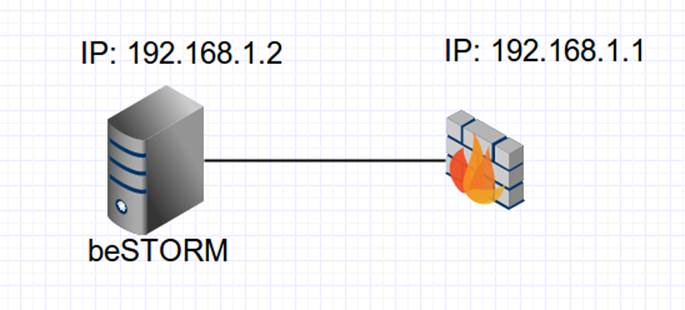
Assign IP addresses to beSTORM server and target firewall like: 192.168.1.2 and 192.168.1.1
Connect the beSTORM server directly to the firewall with a network cable, and no switch in the middle as outlined in the diagram below:
Step 2:
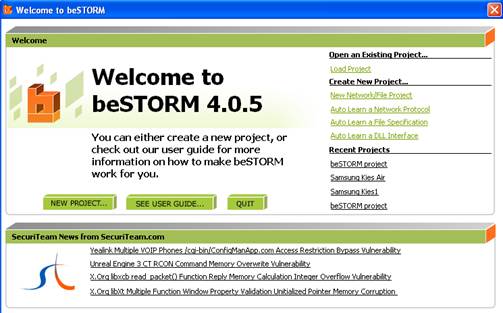
Start beSTORM on the client machine and click on the New Project button:
Step 3:
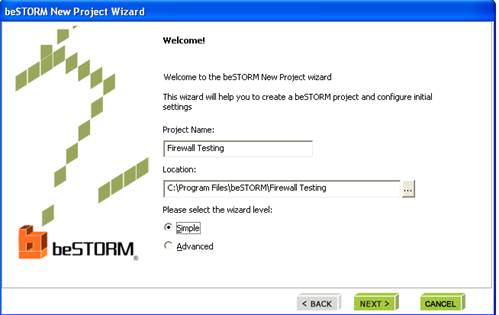
Give the project a name, accept all other defaults and click Next:
Step 4:
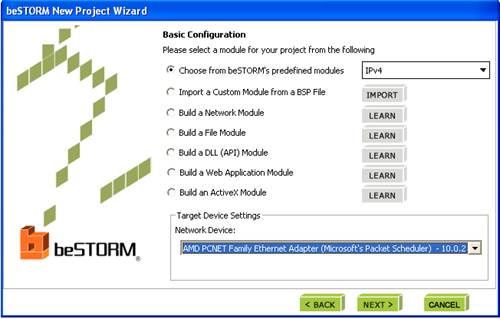
From the list of modules, select IPv4 and select Network Device (Winpcap):
Step 5:
Set the IP address and MAC addresses for server and target:
Destination Address: this is the MAC address of the firewall. To find this value, double-click on the field and a MAC Address Finder helper dialog will appear:
Enter ‘192.168.1.1’ and click ‘Use’. The MAC Address of the firewall should appear. Click ‘OK’ to accept.
Sender IP Address: this is the beSTORM machine IP address
Source Address: This is the MAC address of the beSTORM machine. You can find it using the MAC Address Finder dialog as described above (this time, use ‘192.168.1.2’ which is the IP of the beSTORM machine)
Target IP Address: this is the firewall’s IP address
Step 6:
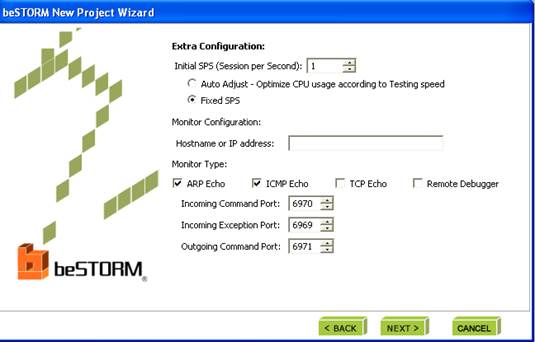
On the ‘Monitor configuration’ page, select ARP Echo and ICMP Echo, and accept all other defaults.
Step 7:
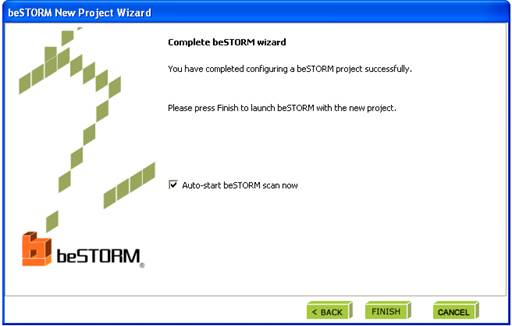
Click ‘Finish’ to end the wizard and save settings as a Project. The testing will start automatically if the Auto-Start box is checked.
Step 8:
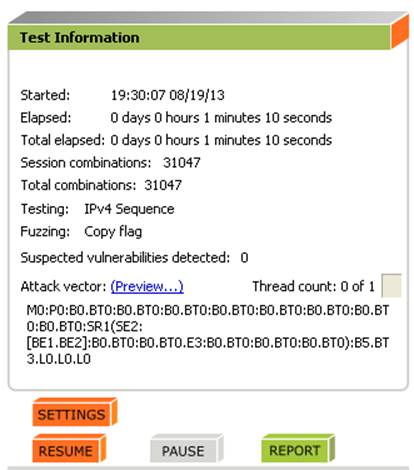
If an exception happens (an attack is successful) a message will pop up briefly to let you know the firewall is not responding.
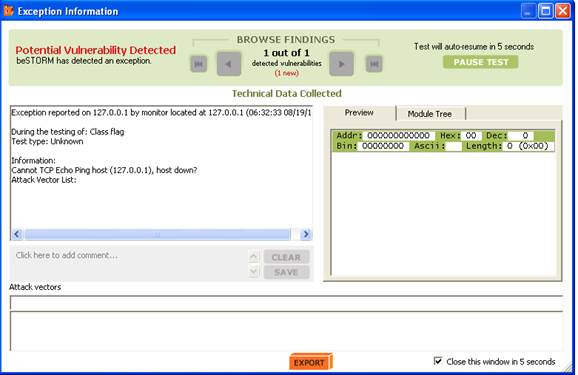
This indicates a possible vulnerability. Testing will resume in 5 seconds unless Pause Test is pressed.
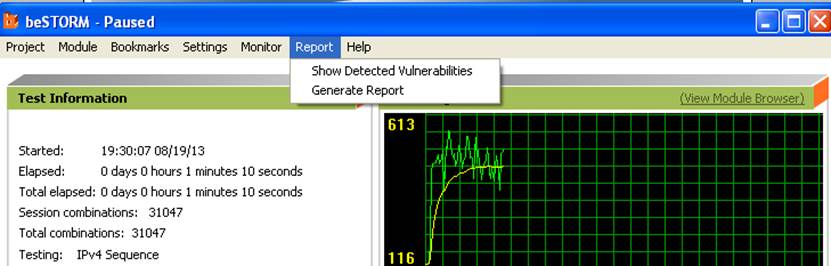
When the testing is finished, click on ‘Report’ to see a short report:
You can also select Report->Generate Report from the menu to generate a more complete report of the testing:
Test #2: Direct test of the firewall (IPv6)
Repeat the tests above, but choose the module IPv6 on Step 4.
Test #3 and #4: Pass-through test of the firewall (IPv4 and IPv6)
Add a third machine, and change the network connections so that the firewall does network routing between the beSTORM server and this new target machine.
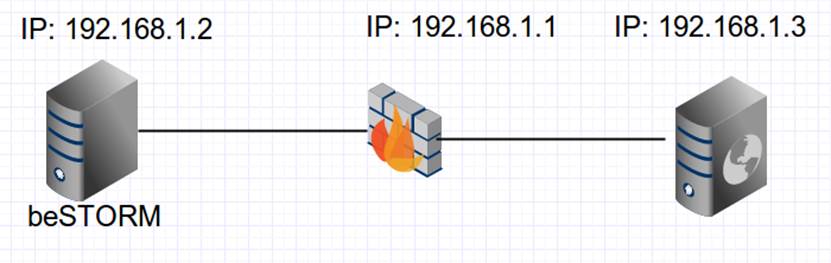
Repeat the two tests above, however note that the ‘target’ is now 192.168.1.3 and not 192.168.1.1 as before. This should be reflected in Step 5, where ‘Target IP Address‘ and ‘Destination Address‘ will now change.
You may want to repeat both ‘direct’ and ‘pass-through’ tests for other protocols supported by the firewall such as:
ARP
TCP
ICMP
UDP
HTTP (if relevant)
DHCP (if relevant)
PDF Application Testing with beSTORM
Step 1:
Create a directory to hold the PDF files. For example:
C:PDF
Make sure your user has permission to write in that directory (for example, open notepad, write something, and save it in C:PDF to see that it can be saved without a permission error)
Step 2:
Run beSTORM
Click on New Project
Give the project a name and click Next
From the list of modules, select PDF. On this same screen, fill in the Output directory to the directory in step 1 (in our example:C:PDF)
Step 3:
Click Next on the Module Environment screen
Step 4:
Click Next to skip the monitor configuration.
Step 5:
Click Finish to start creating the PDF file.
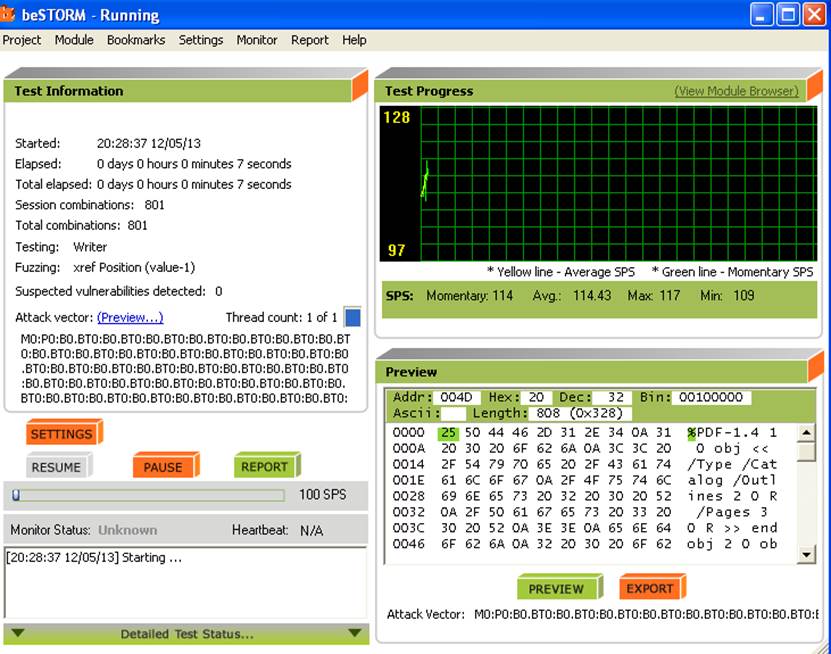
beSTORM will now start running and will create PDF files in the directory C:PDF
NOTE:
To speed up the process, you can pull the SPS slider (on the bottom left of the screen) to increase the file generation speed:

Stop the process (by clicking Pause) when you fill you have enough PDF files. Do not wait for beSTORM to finish since the number of possible PDF files is in the trillions of files.
Step 6:
The directory C:PDF will now have many subdirectories containing PDF files.
All these files are malformed PDF files that will be used to test the PDF application for security holes.
Locate the following .BAT files:
run-filefuzzing.bat
startpid.bat
jitdebugger.bat
thread.bat
These are Windows script files and can be easily change to accommodate your environment. Make the following changes:
run-filefuzzing.bat
1. Locate the line that looks like:
(set threads=T1 T2 T3 T4 T5)(set inputdir=c:jpeg)
change c:jpegto the directory where the PDF files are located (in our case /C:/PDF)
2. Locate the line that looks like:
set appname= c:WINDOWSsystem32mspaint.exe
Change the application name to the path to Acrobat reader on your computer. Make sure to keep the double quotes before and after the full path.
Once you have made these modifications, run
run-filefuzzing.bat
Either from command line or by double-clicking the batch file. If you have configured everything correctly, you should see acrobat reader being opened automatically, loading the PDF files, and automatically shutting down after a few seconds.