Step 1:
Install beSTORM on a machine that is not otherwise in use or on a network.
Confirm or install a network device driver such as Winpcap:
http://www.winpcap.org/install/default.htm
Start NPF service at cmd line: sc start npf
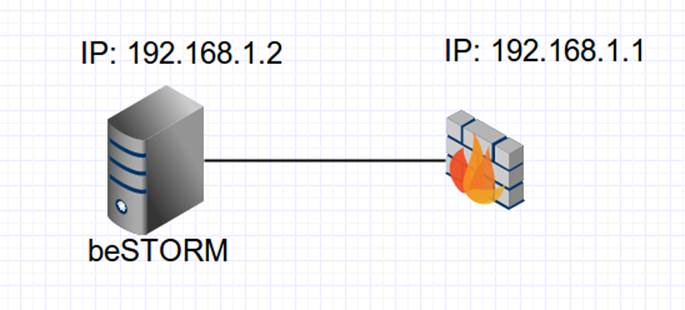
Assign IP addresses to beSTORM server and target IPSEC machine like: 192.168.1.2 and 192.168.1.1
Step 2:
Connect the beSTORM server directly to the IPSEC machine with a network cable, and no switch in the middle as outlined in the diagram below:
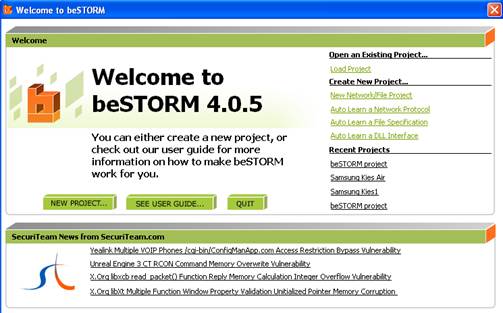
Start beSTORM on the client machine and click on the New Project button:
Step 3:
Give the project a name, accept all other defaults and click Next.
Step 4:
From the list of modules, select IPSEC and select Network Device (Winpcap)
Step 5:
Set the IP address and MAC addresses for server and target:
Destination Address: this is the MAC address of the IPSEC machine. To find this value, double-click on the field and a MAC Address Finder helper dialog will appear:
Enter ‘192.168.1.1’ and click ‘Use’. The MAC Address of the IPSEC machine should appear. Click ‘OK’ to accept.
Sender IP Address: this is the beSTORM machine IP address
Source Address: This is the MAC address of the beSTORM machine. You can find it using the MAC Address Finder dialog as described above (this time, use ‘192.168.1.2’ which is the IP of the beSTORM machine)
Destination IP Address: this is the IPSEC machine’s IP address
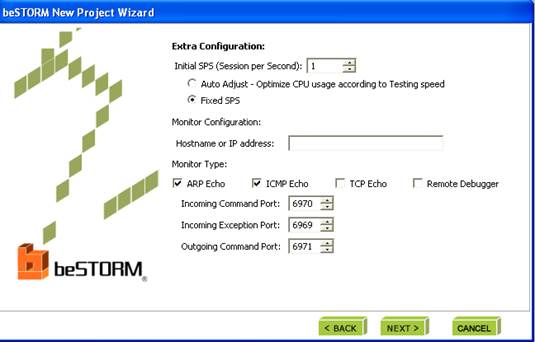
Step 6:
On the ‘Monitor configuration’ page, select ARP Echo and ICMP Echo, and accept all other defaults.
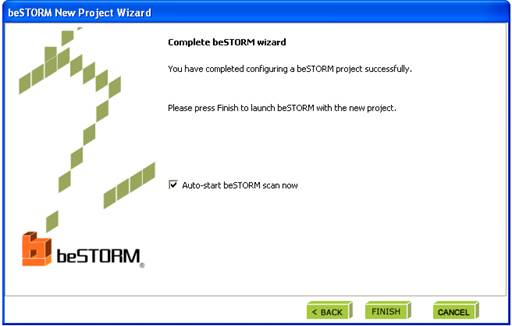
Step 7:
Click ‘Finish’ to end the wizard and save settings as a Project. The testing will start automatically if the Auto-Start box is checked.
Step 8:
If an exception happens (an attack is successful) a message will pop up briefly to let you know the firewall is not responding.
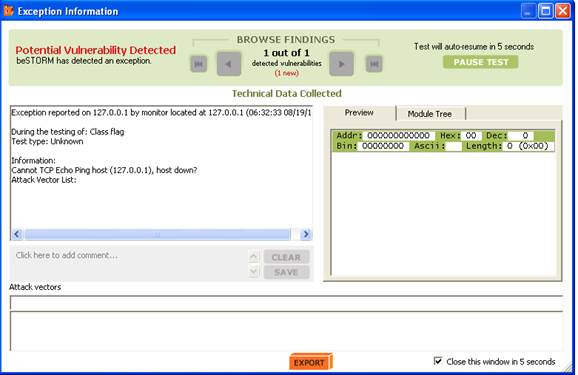
This indicates a possible vulnerability. Testing will resume in 5 seconds unless Pause Test is pressed.
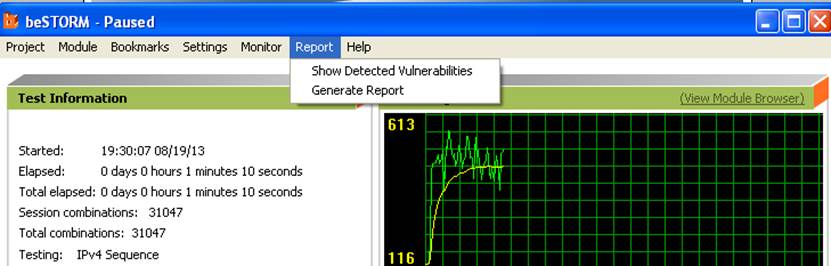
When the testing is finished, click on ‘Report’ to see a short report:
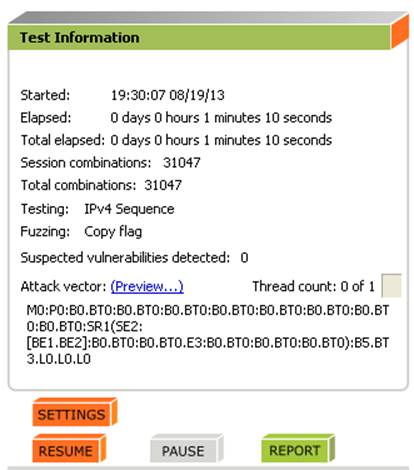
You can also select Report->Generate Report from the menu to generate a more complete report of the testing: